What is Firewall in Computer Network | Packet Filtering Firewall | Proxy Firewall | Circuit Level Gateway | Host Based Firewall | types of firewall in computer network | firewall examples |Types of firewalls
Table of Contents
What is Firewall
A Firewall is a security device to protect your network system or computer from being hacked and malicious attacks by hackers. The firewall product can be hardware or software. Basically it is a system Wall or Boundaries of your computer network that monitors the incoming and outgoing traffic through your network.
It is a security tool that runs on predefined rules set by the user. The user may block or allow access to the system or website through the respective network. it blockes IP ADDESSES, DOMAIN NAME, PROGRAMS, PORTS , KEYWORDS,PROTOCOLS

For example you visit some xyz website and when you click on the website some cookies, unwanted pop-ups and advertisements come automatically if you click on it it can harm your network or Malware can attack your network through viruses That’s why we use firewall which prevents the network from unwanted traffics and unsafe packets which filters the packets and discards the malicious packets before entering your network.
- Provide a Safety Wall between Private Network and the internet or public network .
- Nowadays data security is very important tool of any small or big firm That keeps your data safe.
Types of firewalls.
There are several of Types of firewalls but we will discuss only 4 Types of firewalls which we will describe in the section below.
- Packet Filtering Firewall
- Proxy firewall
- Circuit Level Gateway
- Host Based Firewall
1#. Packet Filtering Firewall
Packet Filters works on IP level it checks incoming data packet which contains SA(Source Address), Destination, Protocol and Port Numbers, Packet filtering operates on a set of firewall rules that restrict user-defined protocols, IP addresses, port numbers, which they continue to block until the rules are changed Basically it is a Network Filter which is filtering the packets being received and sending over the network if it matches the rules that allow packets to enter if not then it will discard the data packet.
Let’s take example and set rules and learn how packet filtering firewall works.
When a user send a request through a network to a private network it will go along with some data packets which include source address, destination address, port number and protocol.
| Source address | Destination | protocol | port | action |
| 170.0.0.1 | 192.168.1.210 | IP | 80 | allow |
| 154.0.0.1 | 192.168.1.210 | IP | 80 | allow |
| 184.0.0.1 | 192.168.1.210 | UDP | 53 | deny |
| 184.0.0.10 | 192.168.1.215 | TCP | 53 | allow |
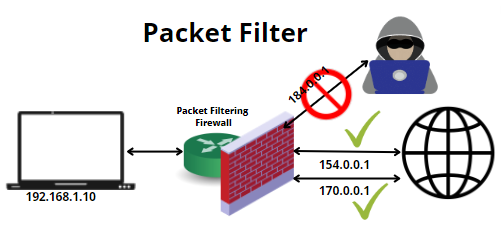
Disadvantage : Less security only checks the Rules it does not check data/payload which can harm your network if some items are downloaded or bypass
2#. Proxy firewall
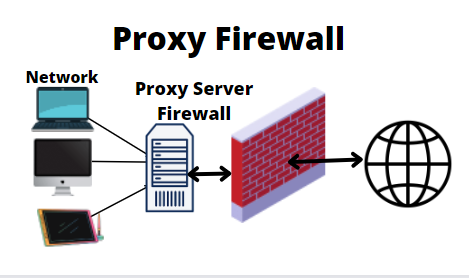
Proxy firewall is also known as Application Level Gateway which is more secure than packet filtering firewall because packet filter is not capable of checking data and payload of data, but in proxy firewall it checks both payload and data and allows data to be sent internal network If the Proxy firewall finds something malicious or harmful, it is immediately discarded or blocked.
Proxy firewall creates an anonymous network for private networks, it has its own IP address, so it only shows the firewall’s IP address and never reveals the actual network details to the world.Which means you never interact directly with private or other networks, you have to go through this firewall to protect and hide your details.
let’s take example you visit a website xyz let’s say your network IP is 172.0.0.1 and firewall IP is 192.168.1.110 so now if xyz checks the receiver data it will show only 192.168.1.110 which is firewall IP Is. you are the 192.168.1.110 for xyz , So if xyz will send you a request it will first receive it through 192.168.1.110 firewall which will check the request and allow or discard the request as per the rules.
3#. Circuit Level Gateway
The circuit level gateway firewall creates a new connection between UDP and TCP and provides security to the network. It works at the session layer of OSI (Open Systems Interconnection) model, it also checks TCP handshaking device for packets coming from trusted device or not from web server.
4#. Host Based Firewall
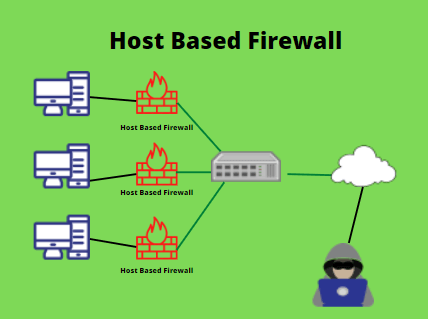
Host based firewall is an operating base system firewall installed by default that protects your system from unauthorized networks, malicious software and malware scripts etc. This firewall is provided to all connected hosts. There is no need to install this type of firewall, it is already installed in the system and it gets updated when your windows is getting updated and third party host based firewall is also available in the market.
Host based firewall Single computer firewall which is installed on only one computer which means each computer has its own host based firewall which is easy to configure but we need to maintain or monitor the configured CPUs one by one. Which is a very long and slow process. It also provides alerts to allow or block both incoming and outgoing connections while checking for any discrepancies,
Also look our Other’s Article :
How to turn off ad Blocker Chrome
How to Check Computer System Information Windows 10
How to turn off antivirus in windows 10
FAQ
What is meant by firewall in the context of computer network.
Firewall is nothing but a Secure Wall for Computer Network that monitors your system and protects it from any malicious, activity and malware attacks by hackers. In other words it is a burning wall that keeps unwanted, unsecured data off the network and allow only trusted devices or networks.
What is Firewall Rules.
Check or Monitor Incoming and Outgoing Traffic.
Allow or Deny the connection.
Provides the Report of destination IP address, Source IP address, Port Number
What is Router firewall
A router firewall is a hardware device that performs security checks on incoming and outgoing traffic through an Internet connection. It provides easy-to-install protection for connected devices. We can set different rules on different systems. for more please visit cisco

nice knowledge about Firewall.Thanks for sharing.
thanks for your comment please keep visiting…
wow very amazing article keep posting